Table 3 from Trusted third party services for deploying secure telemedical applications over the WWW | Semantic Scholar

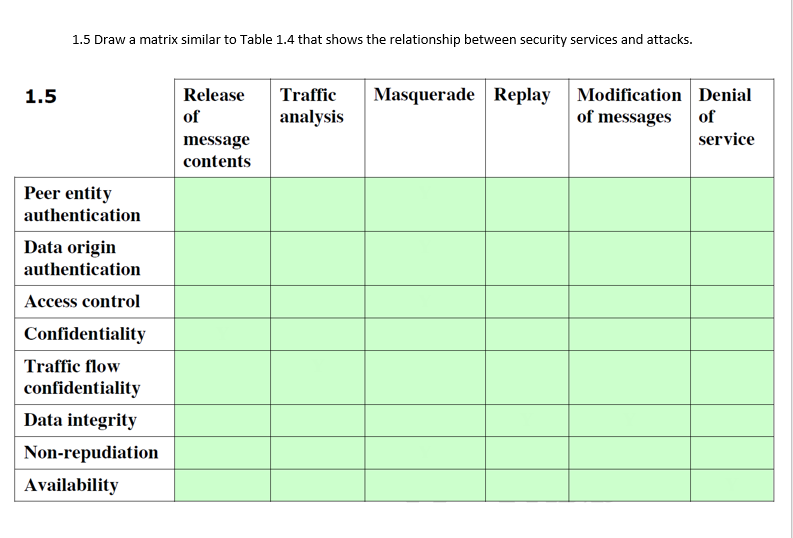
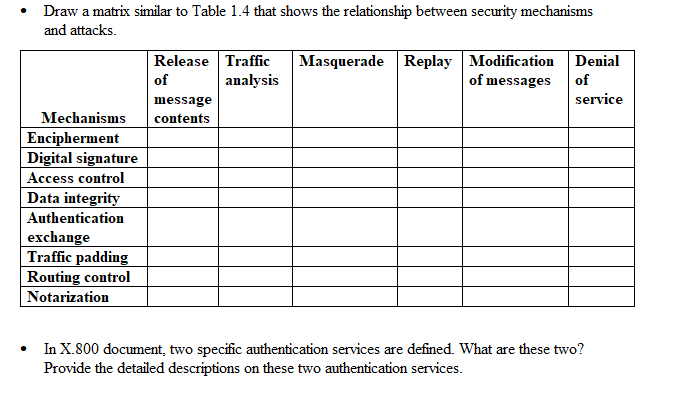
Network security essentials - chapter 1 - 7 Draw a matrix similar to Table 1.4 that shows the relationship between security services and | Course Hero
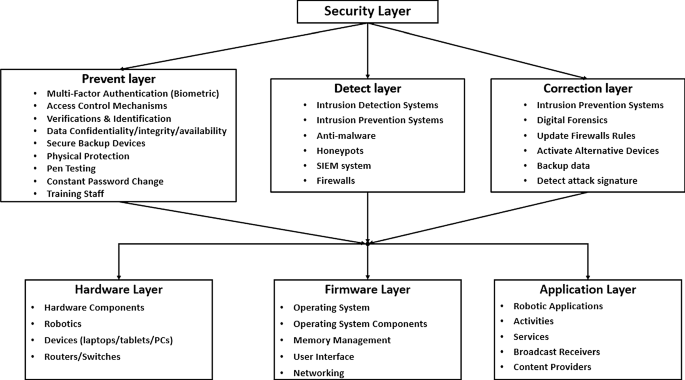
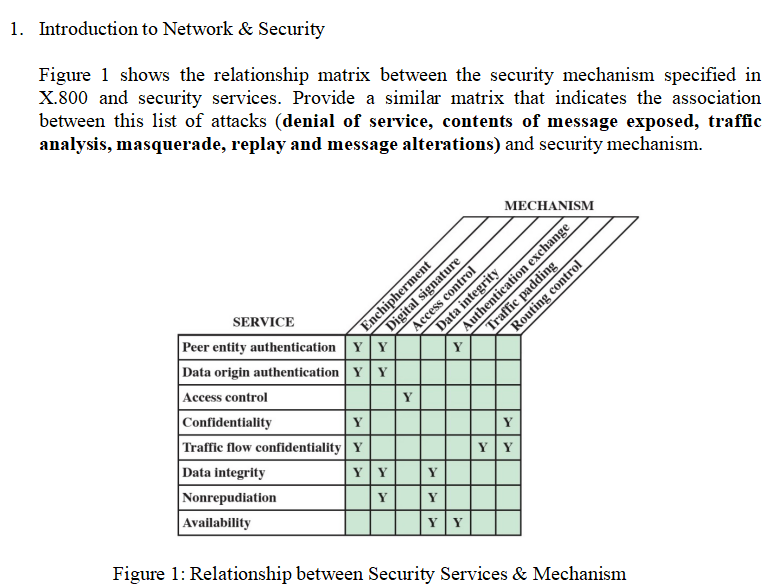
Robotics cyber security: vulnerabilities, attacks, countermeasures, and recommendations | SpringerLink
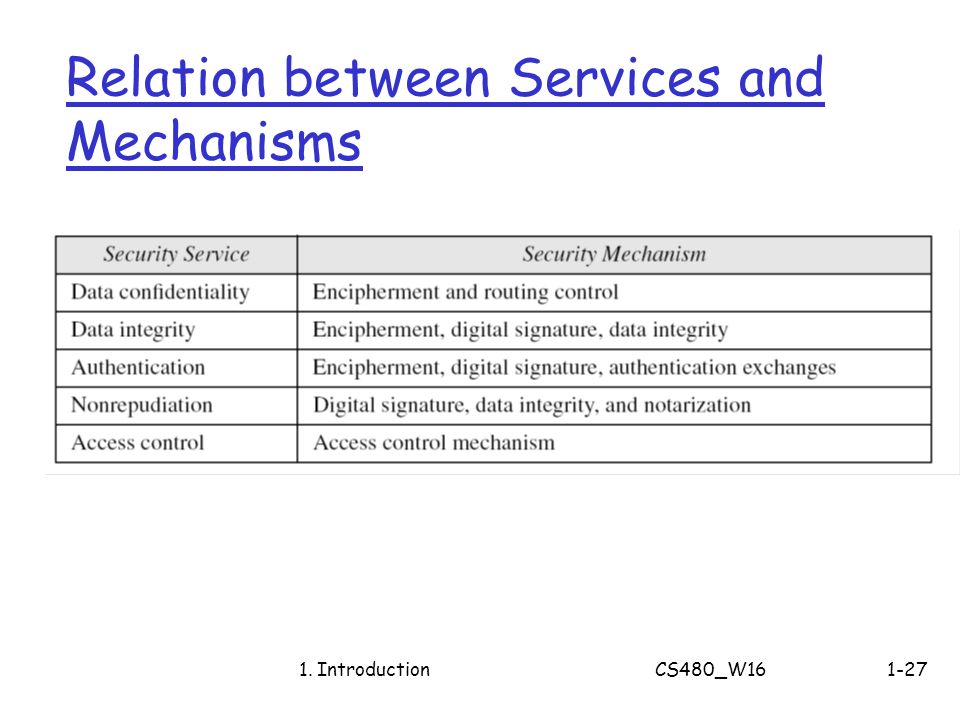
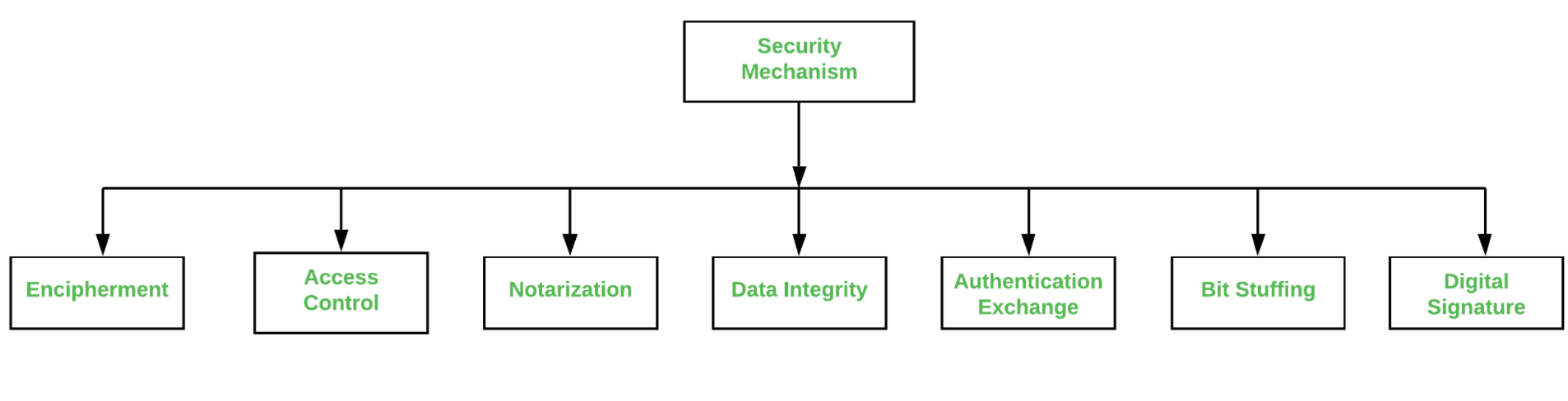
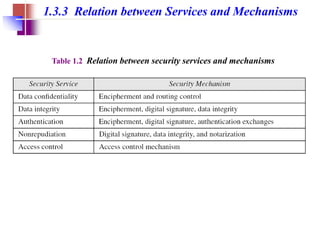
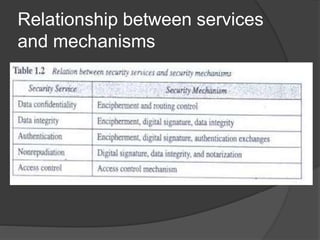
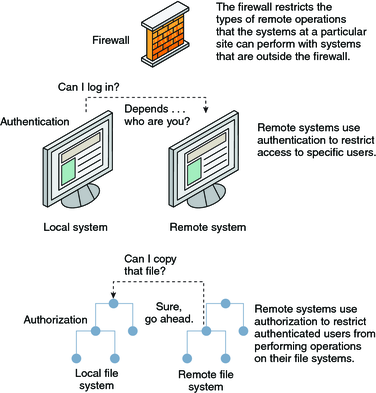
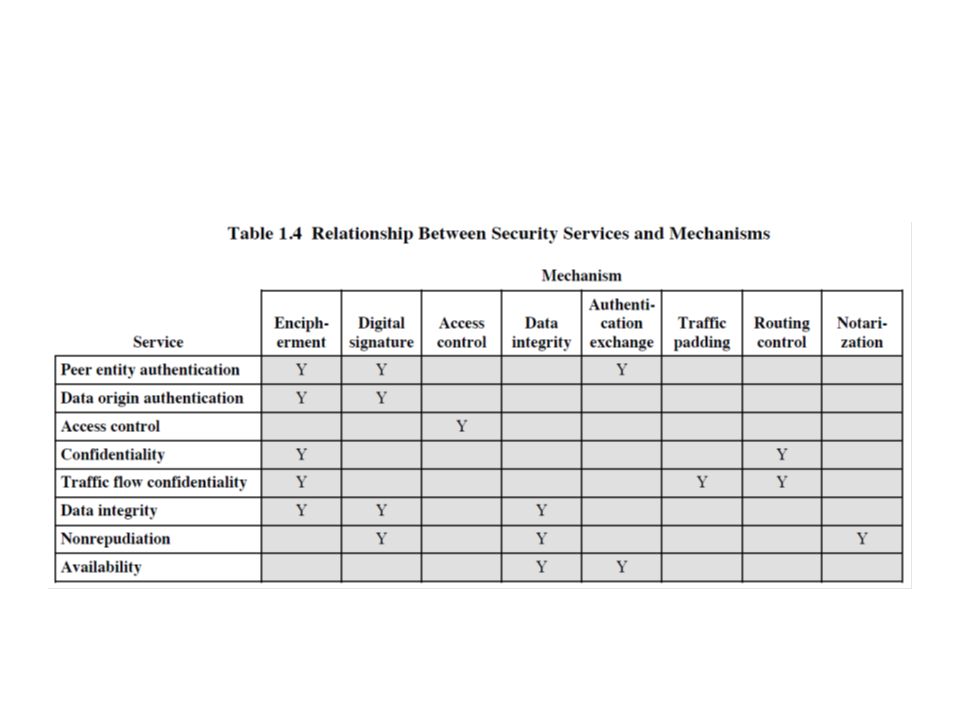
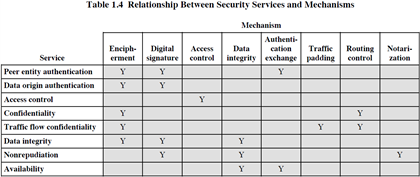
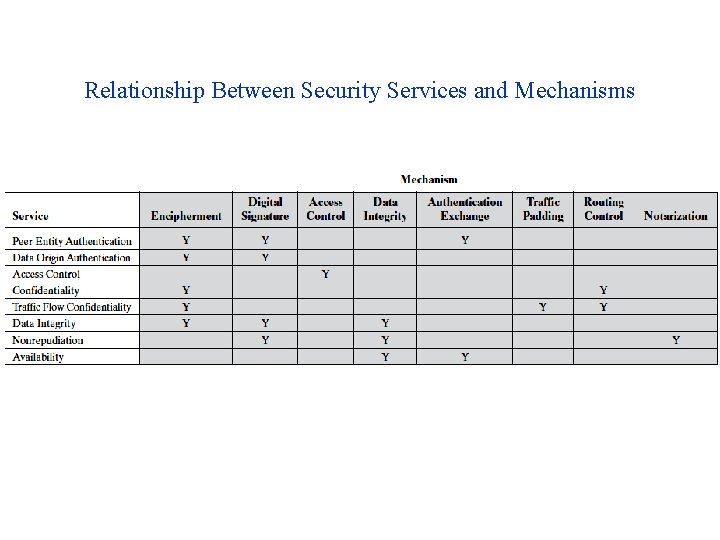
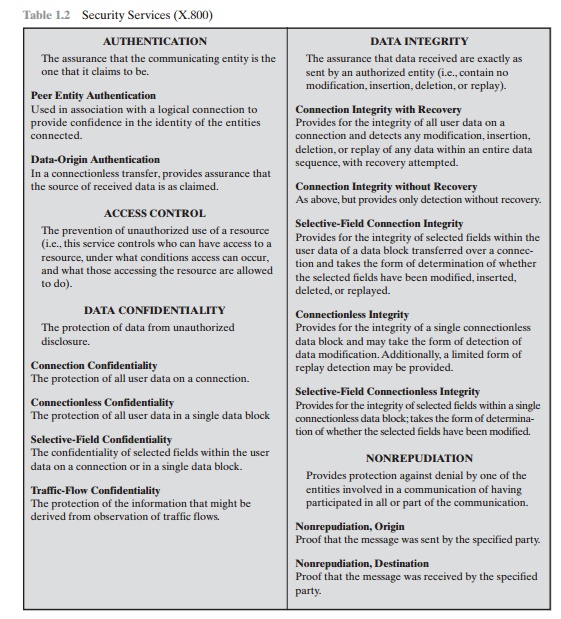
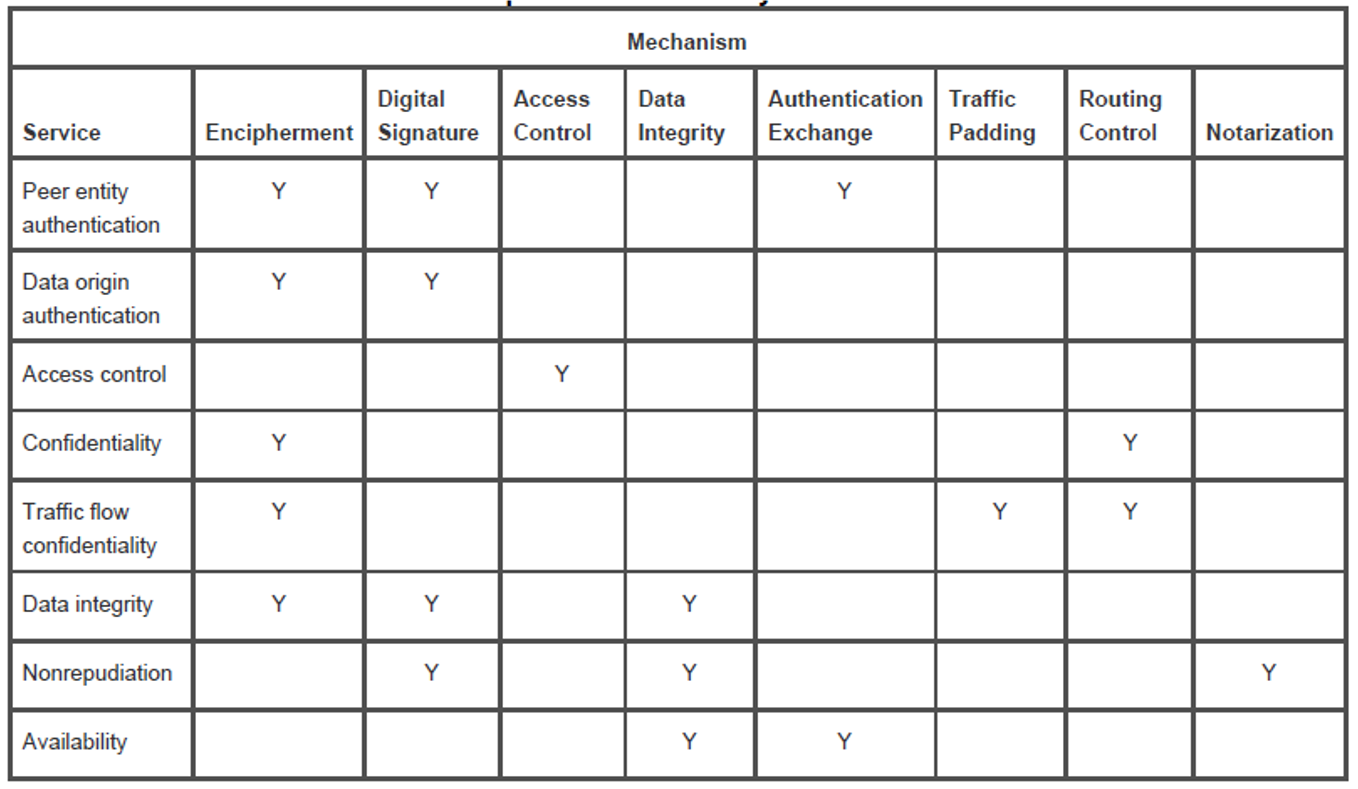
CS480 Cryptography and Information Security Huiping Guo Department of Computer Science California State University, Los Angeles Course administration. - ppt download
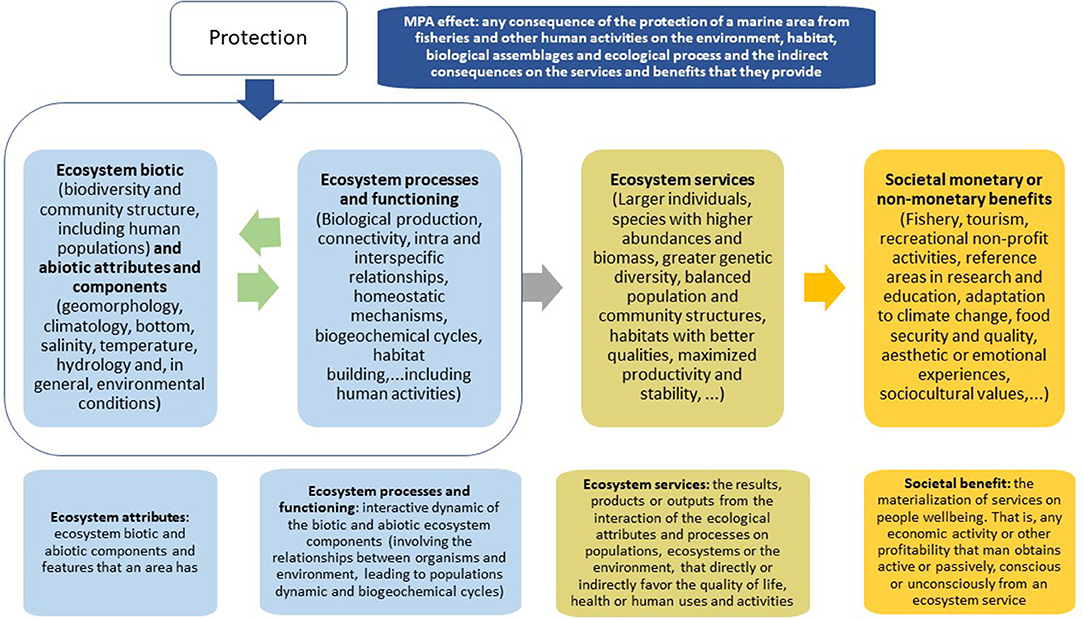
Frontiers | Reviewing the Ecosystem Services, Societal Goods, and Benefits of Marine Protected Areas | Marine Science
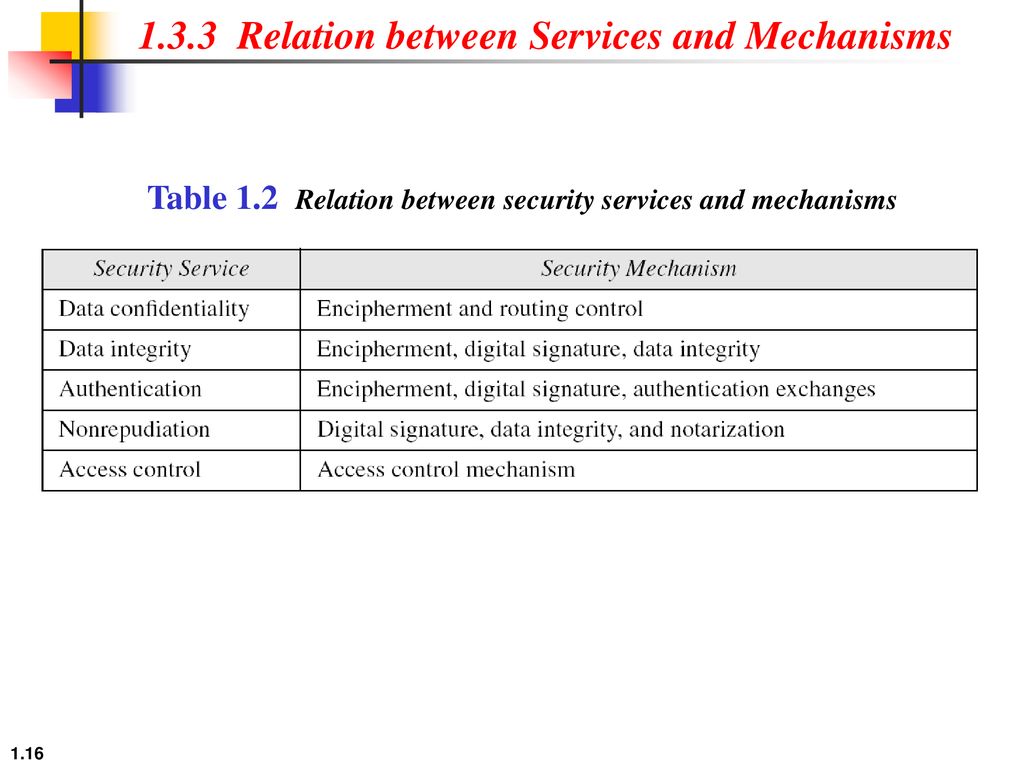
Chapter 1 Introduction Copyright © The McGraw-Hill Companies, Inc. Permission required for reproduction or display. 1.# - ppt download